Research Journey
How our lifecycle analysis of 278,435 vulnerabilities led to ML models that predict exploitation at disclosure
Research Timeline
Transfer Report
AlBedah - ~246K CVEs analyzed through March 2024
- Established CVE-CWE-CPE-Exploit-Patch framework
- Completed sub-objectives 1-6 (lifecycle foundations)
- Identified ML prediction as Future Work
"Longitudinal Vulnerability Lifecycle Analysis"
AlBedah, Gashi, Howe - 278K CVEs (1999-2025)
- Attackers win 75.8% of exploit-patch races
- Gap widened from -58 to +147.9 days (2010-2024)
- 95% same-vendor version overlap
ML Exploitation Prediction
Current Work - 327K CVEs
- 83.0% exploited before CVSS, 85.5% before CPE (6 independent sources)
- Early Premium: AUC 0.9913 with 25 features
- Outperforms full 66-feature model
Lifecycle Findings to ML Features
Each feature in our ML model is grounded in empirical findings from our lifecycle analysis and academic literature. Click any card for detailed justification.
"Attackers win 75.8% of races"
vendor_exploit_rate
Historical exploitation success by vendor
Academic Basis: Shahzad et al. (2012, 2020) vendor patterns
Click for details
"95% same-vendor version overlap"
version_risk_delta
Risk inheritance across versions
Academic Basis: Shahzad et al. (2020) + Garcia et al. (2011) supplementary
Click for details
VLAI: 84.5% CVSS Agreement
desc_similarity_max
17.9% importance - most predictive
Academic Basis: Suciu & Dumitras (EE) + VLAI (Bonhomme & Dulaunoy 2025)
Click for details
"SQL Injection: 91% to 40%"
cwe_ids
CWE-stratified exploitation rates
Academic Basis: MITRE CWE framework
Click for details
"Gap widened to +147.9 days"
exploit_patch_gap
Time window of vulnerability
Academic Basis: Frei (2009) "gap of insecurity"
"83.0% before CVSS, 85.5% before CPE"
Early Premium Model
25 day-0 features, AUC 0.9913
Source: NVD history database (4M+ records)
The "Aha!" Moment
The Problem
83.0% exploited before CVSS, 85.5% before CPE (6 independent sources)
The Question
How to predict WITHOUT waiting for NVD?
The Answer
Day-0 features: vendor history + description similarity
Result: Early Premium (AUC 0.9913) outperforms full model!
Key Visualizations
Click any figure to view larger with resize options
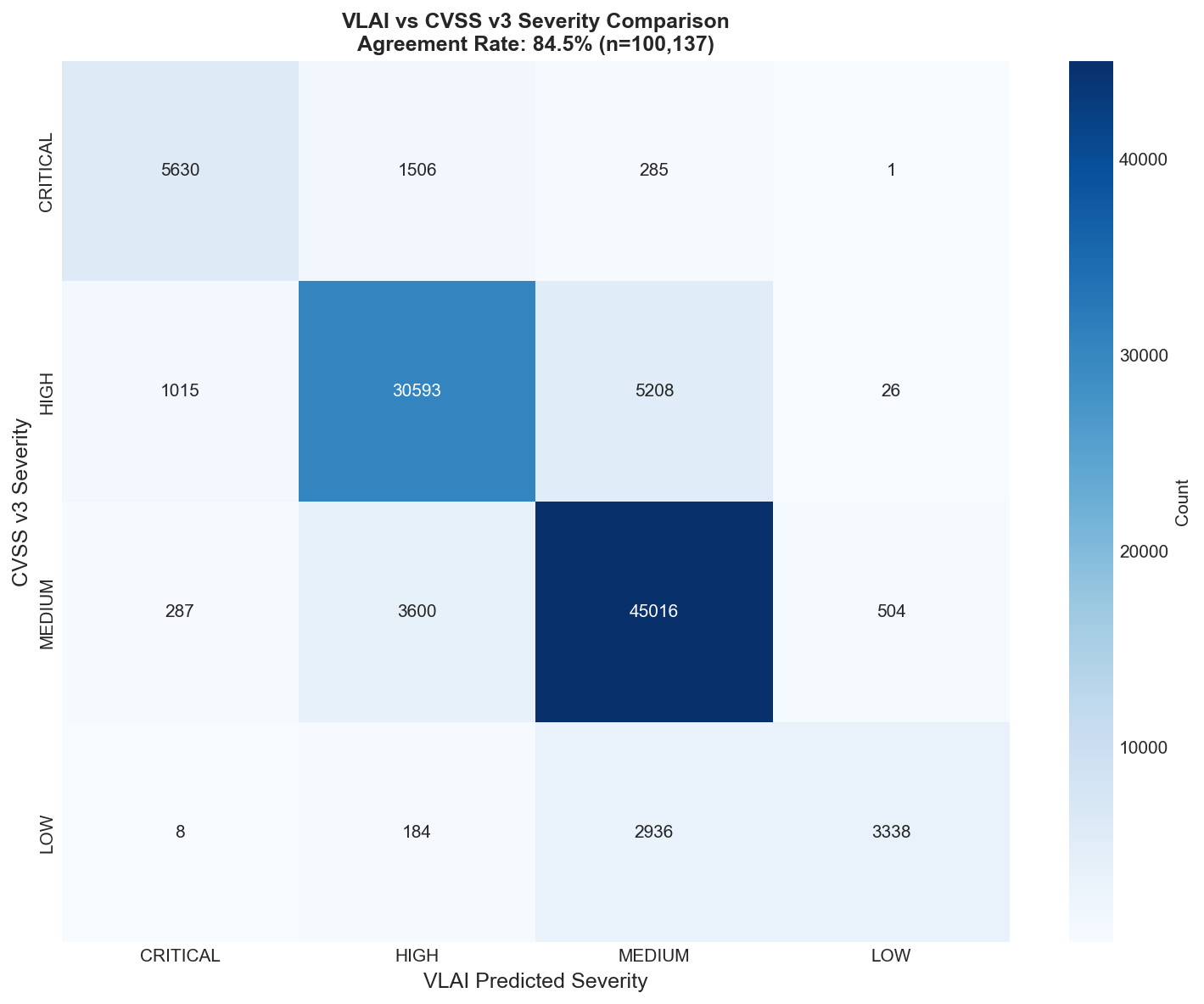
VLAI-CVSS Agreement
84.5% agreement validates text-based prediction
Click to enlarge
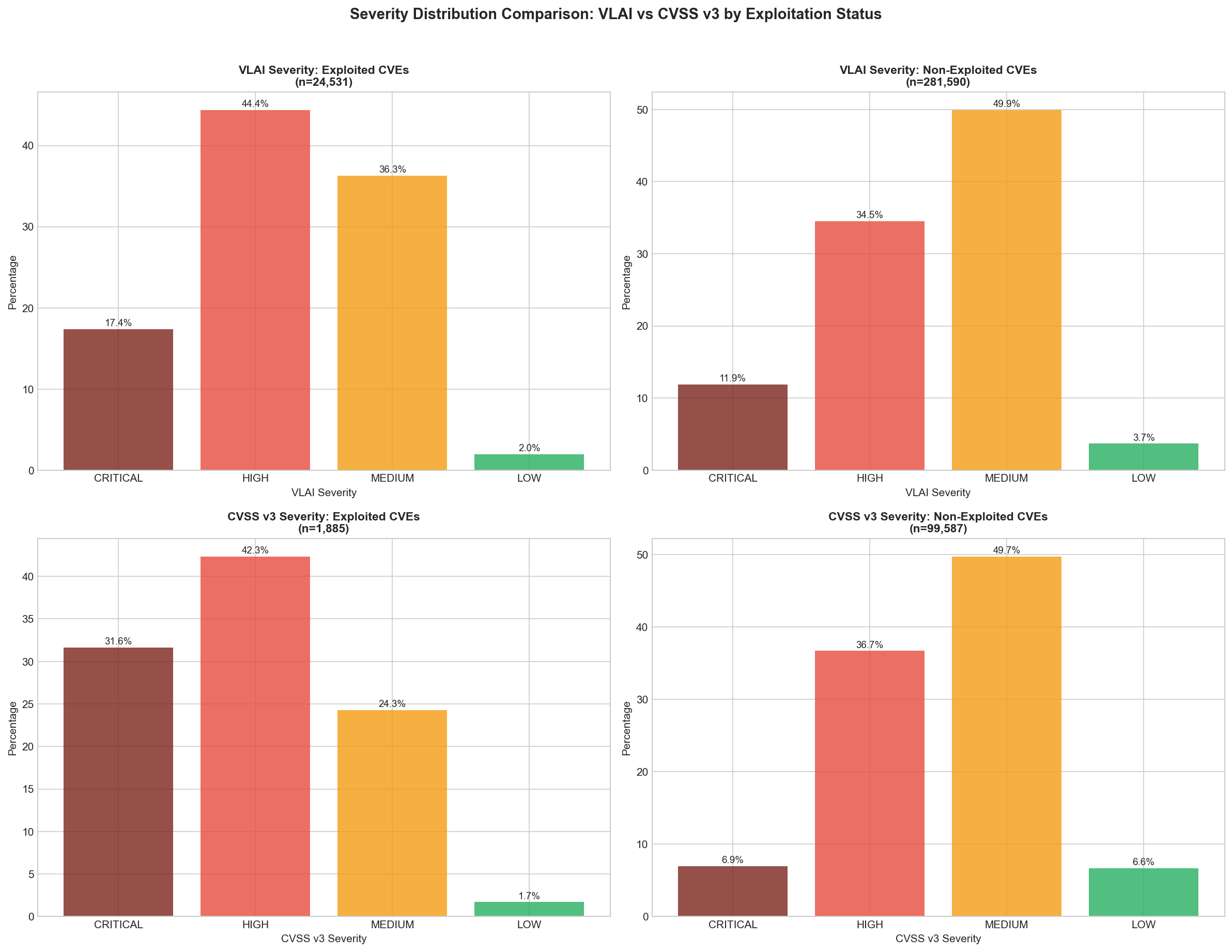
VLAI Severity Distribution
Severity patterns in exploited CVEs
Click to enlarge
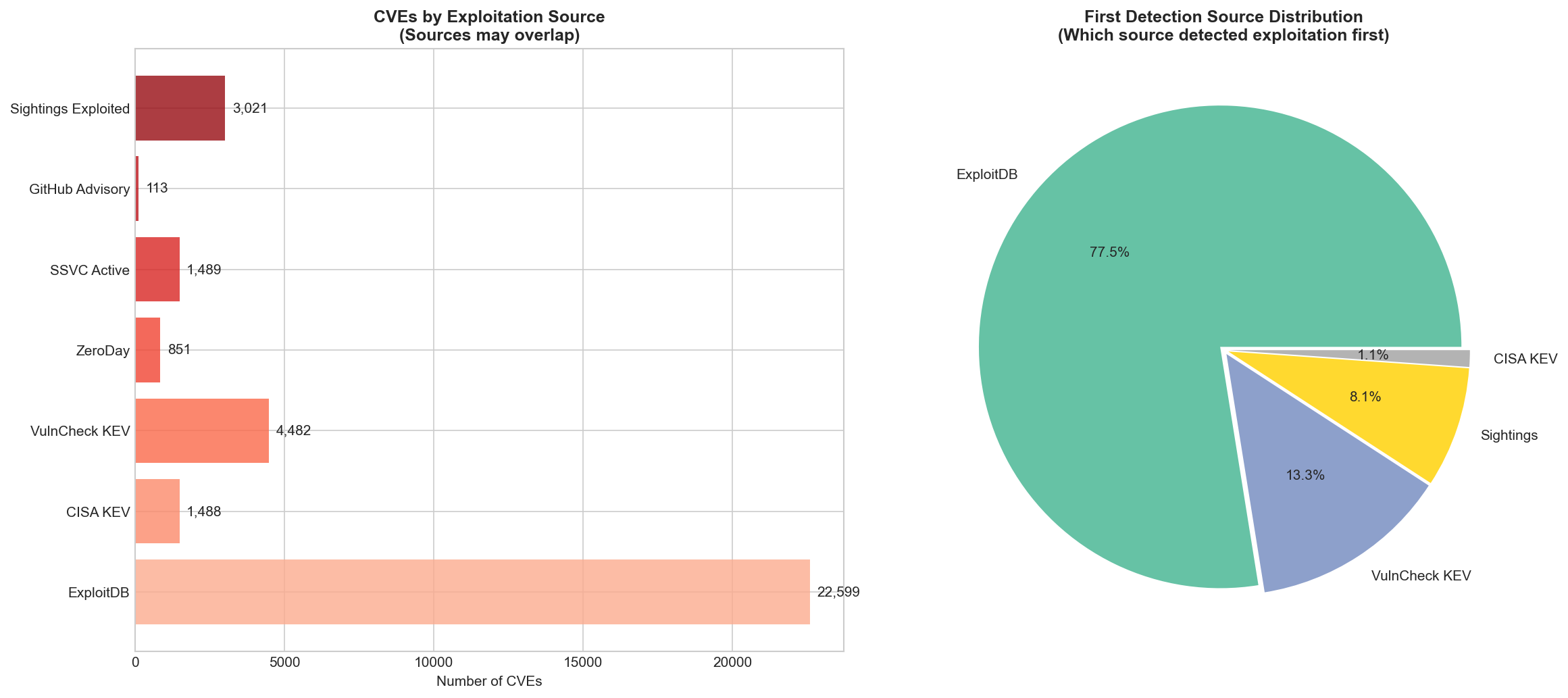
Exploitation Sources
7 sources (6 independent + NVD exploit tags) consolidated for ground truth
Click to enlarge
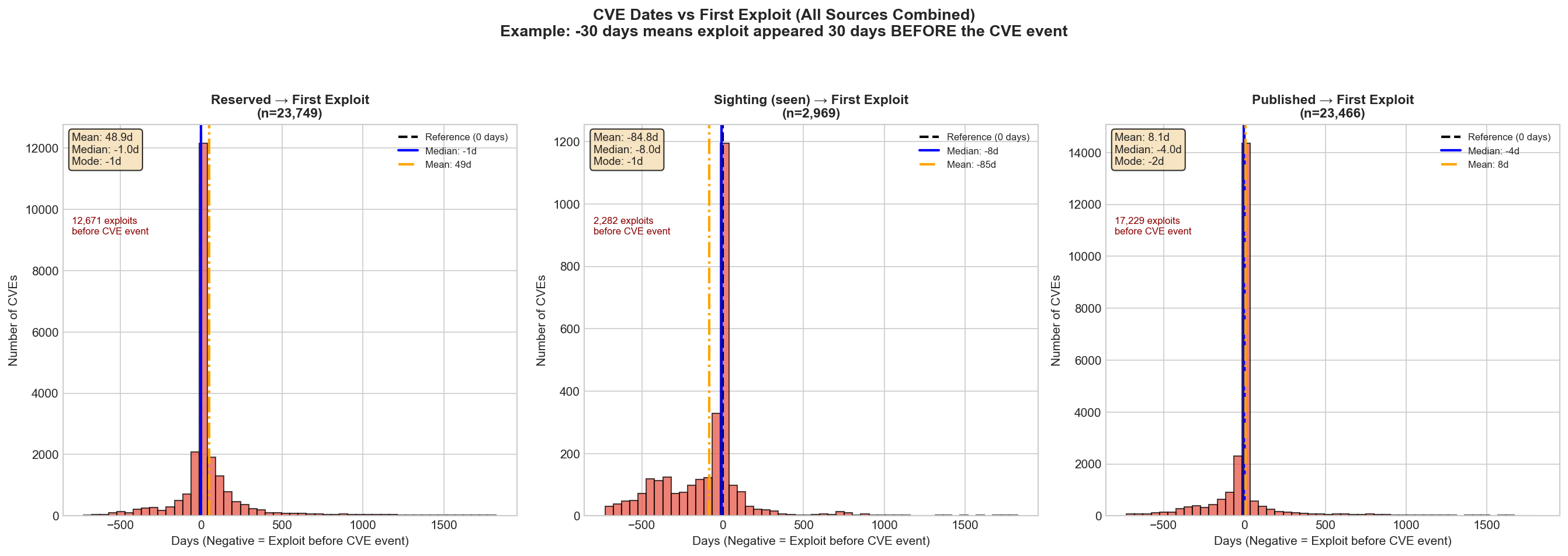
Lifecycle Analysis
CVE dates vs first exploit timing
Click to enlarge
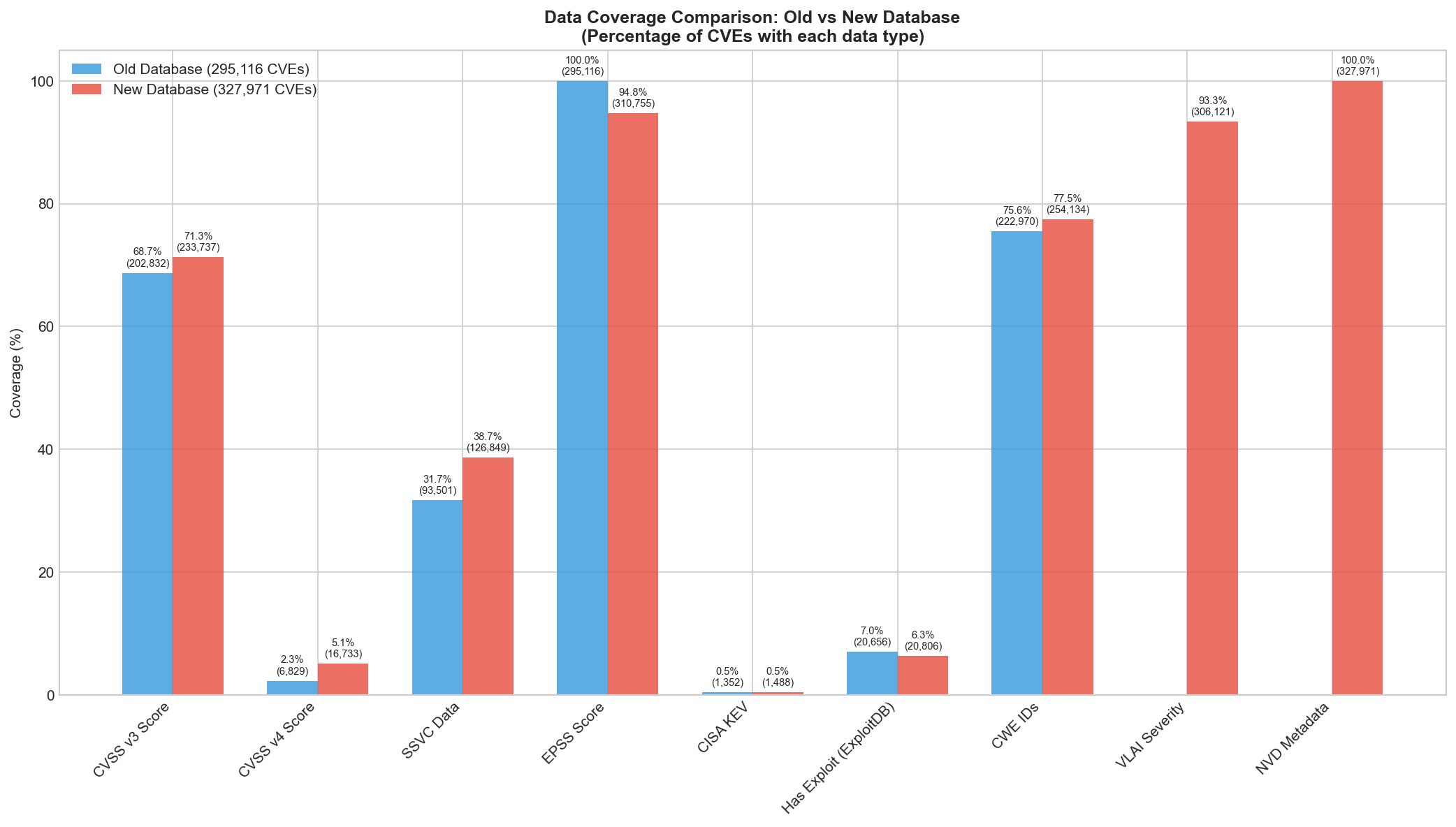
Data Coverage
Coverage comparison across sources
Click to enlarge
Feature Importance
Early Premium model top features
Click to enlarge
Early Premium ROC
AUC 0.9913 performance curve
Click to enlarge
CWE Exploitation Rates
Exploitation by vulnerability type
Click to enlarge
Vendor/Product Features
Risk inheritance visualization
Click to enlarge
Academic Foundation
Our Prior Work
-
AlBedah (2024) - Transfer Report
Framework for CVE-CWE-CPE-Exploit-Patch analysis (~246K CVEs)
-
AlBedah, Gashi, Howe (2025) - "Longitudinal Vulnerability Lifecycle Analysis"
278K CVEs: 75.8% attacker wins, +147.9 day gap acceleration
Key Academic Precedents
-
Shahzad et al. (2012, 2020)
Multi-dimensional vulnerability characterization (56K CVEs)
-
Suciu & Dumitras - Expected Exploitability
Dynamic exploitation risk from text features
-
VLAI (Bonhomme & Dulaunoy 2025)
RoBERTa severity prediction: 84.5% CVSS agreement
-
Garcia et al. (2011) (supplementary)
OS diversity for intrusion tolerance
Experience the ML models built from these research findings